Setting up my blog as an Onion service (Tor hidden service)
Written on
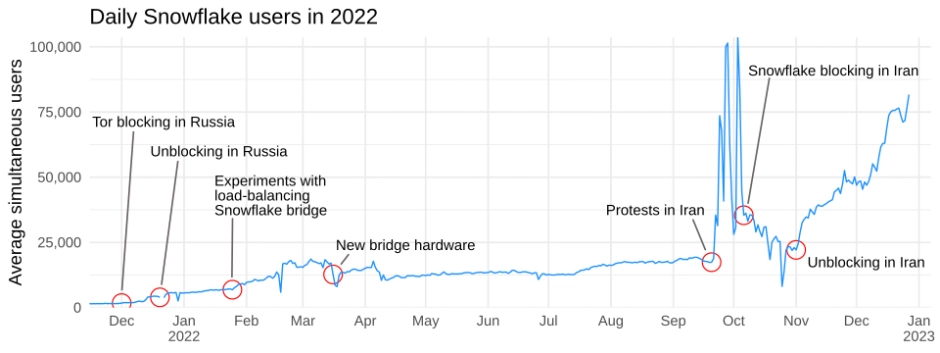
If you don’t know about it, Tor is a software that helps online privacy and fights censorship using the Onion network. For example, tens of thousands of people in Iran and Russia are using Tor through Tor’s Snowflake proxies to get around government censorship and access vital information, as news organizations like the BBC started offering access through Tor. As online services are happy to turn over our data to the authorities, it is crucial for Tor to exist so journalists, activists, whistle-blowers, and anyone living under oppressive regimes can access information and communicate freely.
But there is really no reason for Tor to be used solely by people trying to avoid censorship or stay private. In fact, I think it is good for people to use Tor for other things, because this way Tor is not just a tool for “people with something to hide” but a tool that everyone uses. It’s a bit like adding pronouns in your bio on social media: it’s good when cis people put pronouns in their bios because otherwise just having your pronouns in your bio would immediately flag you as a trans or gender nonconforming person. Everyone else joining in gives security to those who really need it.
Setting up the Onion service
My first step was to set up a Docker container to run Tor in. I put this container on DockerHub for others to use: seriousbug/tor.
Next, I used mkp224o to get a vanity
address. Onion addresses are made out of long, random sequences like
xbbubmuxby...qd.onion, but you can try to generate one that starts with a
special prefix, for example DuckDuckGo has an Onion service that starts with
“duckduckgo”: duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion.
Doing this is computationally expensive, but short prefixes are easy to
generate. I wanted something that starts with bgenc, which only took a few
seconds. I also tried kaanbgenc but gave up after waiting several minutes: the
difficulty goes up exponentially the longer the prefix you want is, so 9
characters would have likely taken months on my desktop.
Next, I set up the configuration file for Tor. That looks like this:
Log notice stdout
HiddenServiceDir /etc/tor/service
HiddenServicePort 80 unix:/var/run/tor/bgenc.net.sockI put the keys that mkp224o generated into a subfolder named service next to
my Tor config. These are going to be mounted at /etc/tor in the Tor container.
I then told Tor to look at /var/run/tor/bgenc.net.sock, where I’ll be mounting
my nginx unix socket at.
And that reminds me, it’s time to set up nginx! Under the server block that
serves my website, I added my onion address as one of the host names:
server_name bgenc.net;
server_name bgenc2iv62mumkhu2p564vxtao6ha7ihavmzwpetkmazgq6av7zvfwyd.onion;Then, I added the listen directive to create and listen to that socket:
listen 443 ssl http2;
listen unix:/var/run/nginx/bgenc.net.sock;I’m using a unix socket here because my nginx is actually running on the base system without a container, while tor is in a container. So to allow Tor to connect to the nginx in the host, I would have had to allow the tor container to use the host network. But I can get around that with a Unix socket, because the socket can get mounted from the host into the container.
Also mind that I’m not using SSL or http2 for the unix socket. There are very few
SSL key services that support Tor, and it’s not necessary anyway because the Tor
network provides the same security guarantees to you already. I also found that
http2 does not work, though I’m not sure why.
I finally added the tor container to a docker-compose.yml to make it easier to
rebuild if needed. That looks like this:
tor-hidden-service:
image: seriousbug/tor
restart: always
volumes:
- ./tor:/etc/tor
- /var/run/nginx:/var/run/torI also needed to make the tor directory with the configuration file and services owned by root, and use 700 as the file permission. Otherwise Tor refuses to start.
Once all of this is set up, I restarted nginx and my Tor container. And that was about it! The website is now accessible through Tor! You can find it at bgenc2iv62mumkhu2p564vxtao6ha7ihavmzwpetkmazgq6av7zvfwyd.onion.
